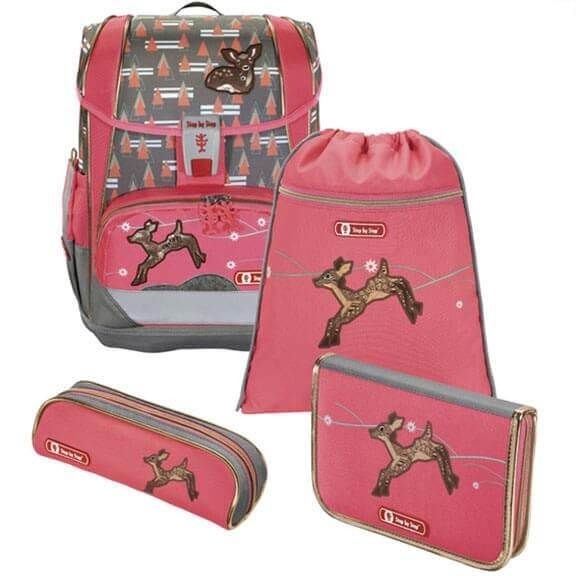
Školní aktovka hama LIGHT 2 pro prvňáčky - 4-dílný set, Step by Step Lesklý Motýl, certifikát AGR + Dárek ZDARMA - www.e-prvnacek.cz

Školní aktovka LIGHT - 4-dílný set, Step by Step Jednorožec, certifikát AGR | Školní aktovky a batohy

Školská taška aktovka hama light srdce srdiečko, - 57 € od predávajúcej pecenahusa | Bazár - Modrý koník

Školní aktovka LIGHT 2 pro prvňáčky – 4-dílný set, Step by Step Lesklý Motýl, AGR – Školní aktovky a batohy

Školní aktovka Hama - Step by Step - LIGHT - Jednorožec - 4 dílný set | Kancelářské potřeby a papírnictví

Školní aktovka hama LIGHT 2 pro prvňáčky - 4-dílný set, Step by Step Lesklý Motýl, certifikát AGR + Dárek ZDARMA - www.e-prvnacek.cz